Authentication & Access Configuration
Configure login-sensitive scans using access profiles so runs can traverse protected pages safely.
Why it matters
Without correct access configuration, scans can fail early or collect incomplete coverage.
Auth configuration ensures data quality for protected environments.
Step-by-step
- Open Run a Scan and expand Access.
- Select access mode (
none,basic,headers,cookie, or form-based when available). - Enter required credentials/headers securely.
- Save as project defaults for repeated runs.
- Validate by running a short scan first.
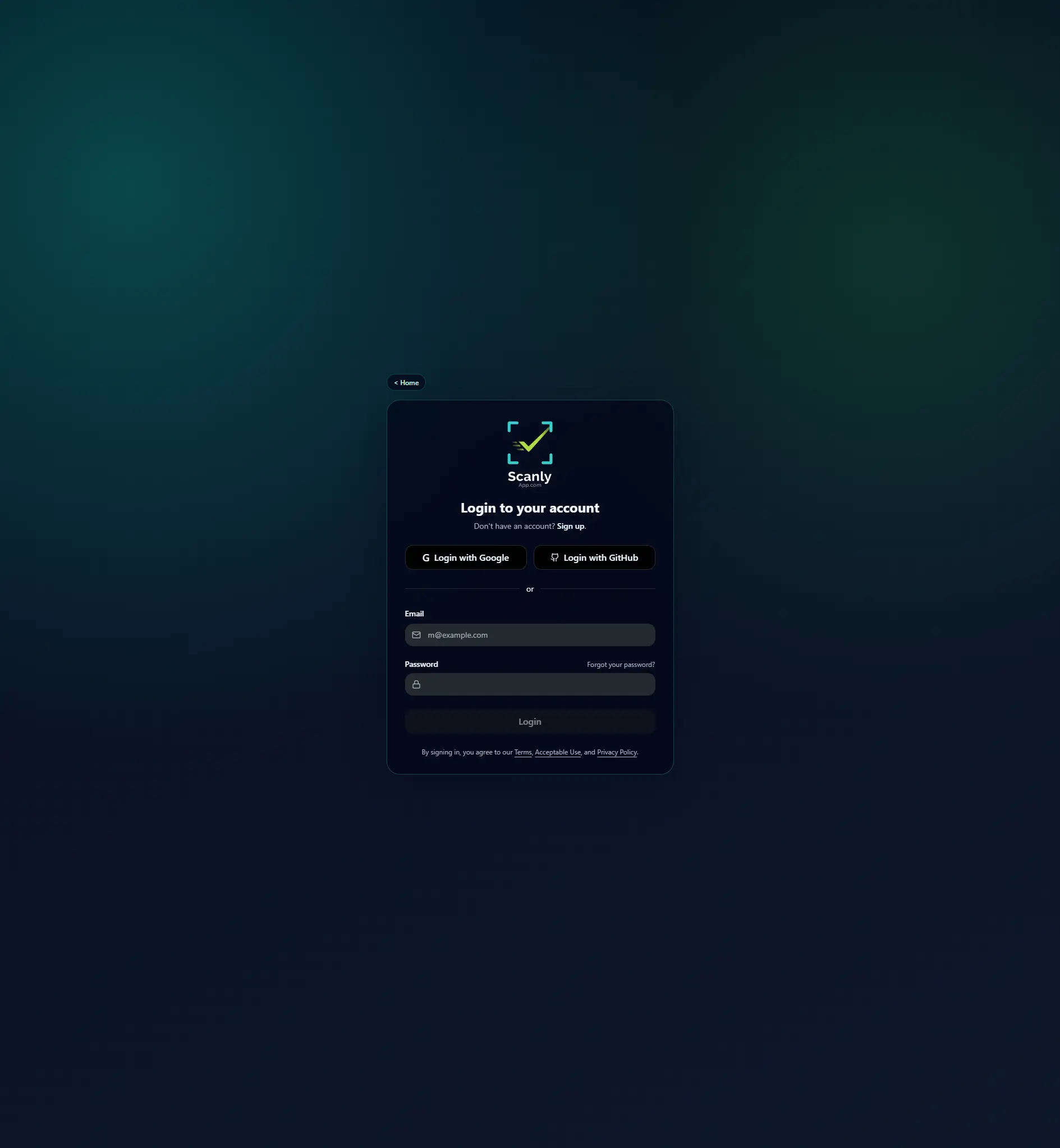
Visual reference
Common mistakes
- Expired cookies or tokens left in saved defaults.
- Header key typos causing silent access denials.
- Reusing privileged credentials across unrelated environments.